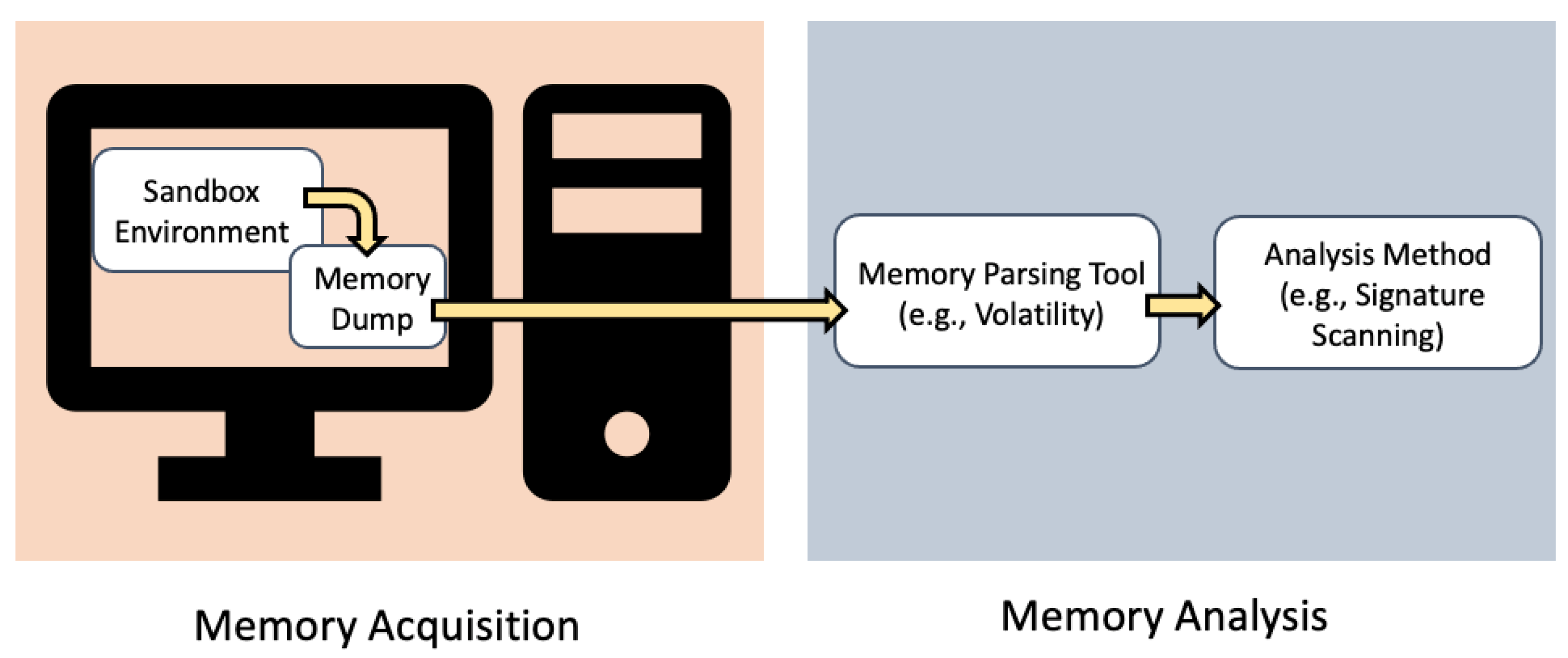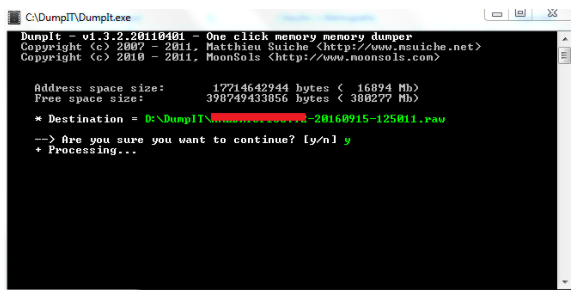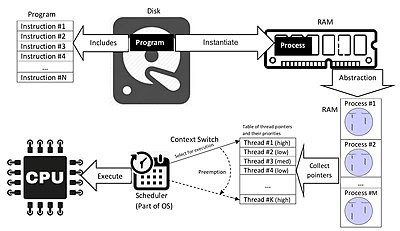
Digging up memories – a deep-dive into memory forensics in the Cyber Security Essentials meetup | Nixu Cybersecurity.

Signature based volatile memory forensics: a detection based approach for analyzing sophisticated cyber attacks | SpringerLink